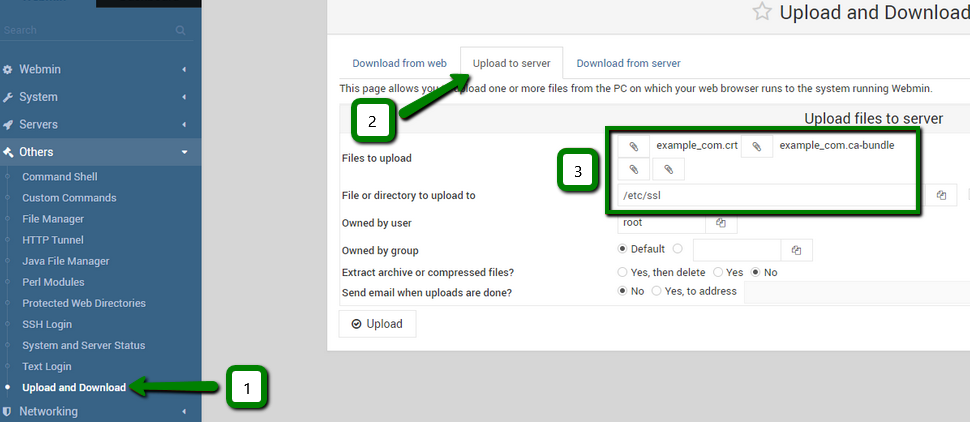
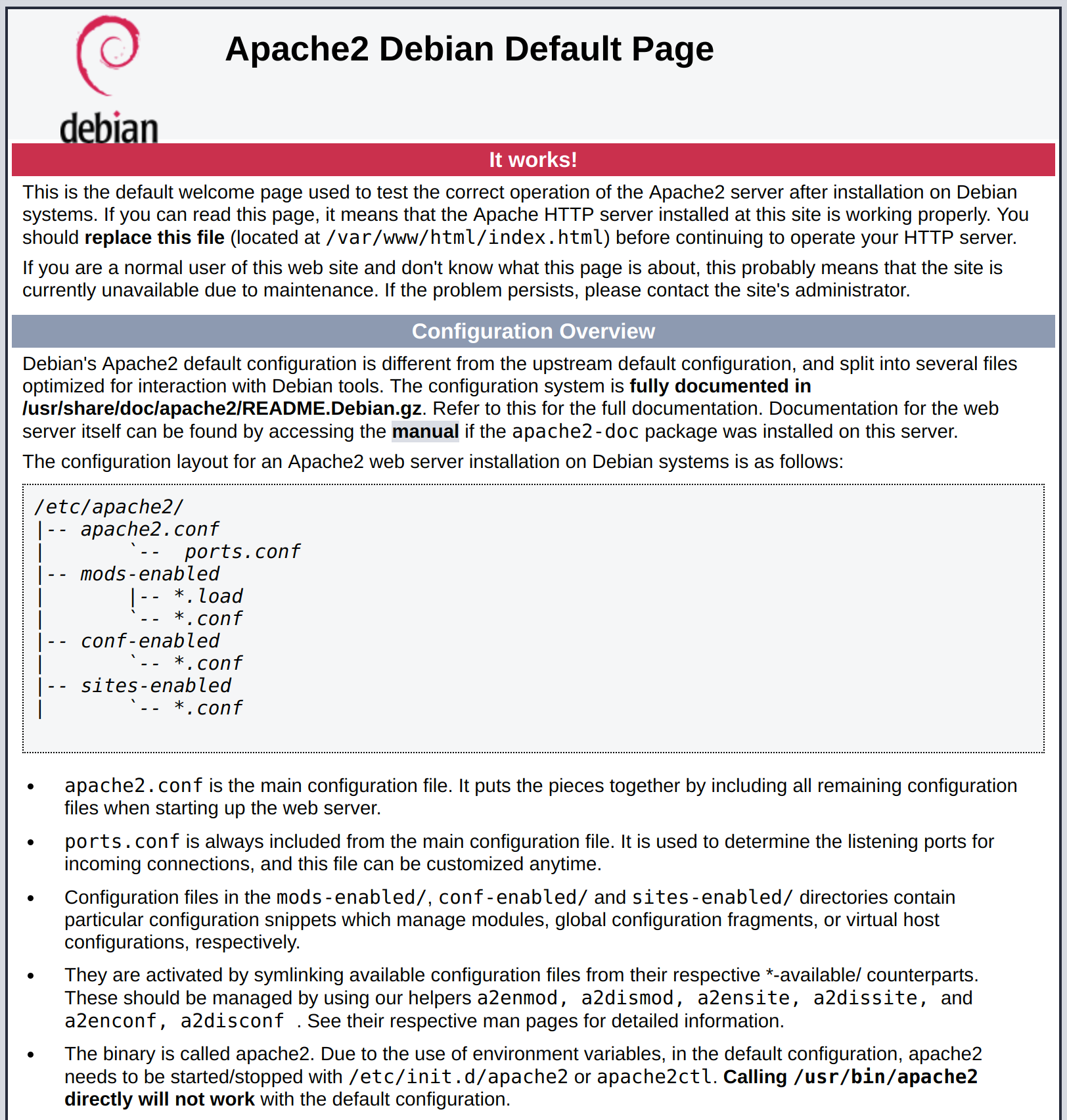
Here is a short note on how to configure Apache to use a certificate file for SSL or How to enable https in Apache httpd server. After you enable SSL in the web server configuration, you should be able to access the application using https. Install The modssl Plugin. Make sure that modssl is installed. The reason is: the Apache web server needs access to the SSL certificate, the private key, and an intermediate CA (Certifying Authority) certificates if applicable. For modularity, it is better to separate the components into separate directories. The SSLCertificateFile and SSLCertificateKeyFile directives in the SSL.conf file must point to the corresponding certificate and key files. If you are using Apache virtual host feature, each virtual host you want to secure must have its own private key and server certificate. Generate a Private Key SSL uses keys to encrypt and decrypt messages. Create a CSR using OpenSSL & install your SSL certificate on your Apache server Use the instructions on this page to use OpenSSL to create your certificate signing request (CSR) and then to install your SSL certificate on your Apache server. SSLCertificateKeyFile /usr/local/apache/conf/ssl.key/domainname.key (or server.key) Note: Some instances of Apache will store Virtual Host information in an ssl.conf file. If your httpd.conf.
OCSP Stapling
The Online Certificate Status Protocol (OCSP) is a mechanism fordetermining whether or not a server certificate has been revoked, and OCSPStapling is a special form of this in which the server, such as httpd andmod_ssl, maintains current OCSP responses for its certificates and sendsthem to clients which communicate with the server. Most certificatescontain the address of an OCSP responder maintained by the issuingCertificate Authority, and mod_ssl can communicate with that responder toobtain a signed response that can be sent to clients communicating withthe server.
Because the client can obtain the certificate revocation status fromthe server, without requiring an extra connection from the client to theCertificate Authority, OCSP Stapling is the preferred way for therevocation status to be obtained. Other benefits of eliminating the communication between clients and the Certificate Authority are that theclient browsing history is not exposed to the Certificate Authority andobtaining status is more reliable by not depending on potentially heavilyloaded Certificate Authority servers.
Because the response obtained by the server can be reused for all clientsusing the same certificate during the time that the response is valid, theoverhead for the server is minimal.
Once general SSL support has been configured properly, enabling OCSPStapling generally requires only very minor modifications to the httpdconfiguration — the addition of these two directives:
These directives are placed at global scope (i.e., not within a virtualhost definition) wherever other global SSL configuration directives areplaced, such as in conf/extra/httpd-ssl.conf for normal open source builds of httpd, /etc/apache2/mods-enabled/ssl.conffor the Ubuntu or Debian-bundled httpd, etc.
The path on the SSLStaplingCache directive(e.g., logs/) should match the one on the SSLSessionCache directive. This path is relativeto ServerRoot.
This particular SSLStaplingCache directive requiresmod_socache_shmcb (from the shmcb prefix on thedirective's argument). This module is usually enabled already forSSLSessionCache or on behalf of some module other thanmod_ssl. If you enabled an SSL session cache using a mechanism other than mod_socache_shmcb, use that alternativemechanism for SSLStaplingCache as well. For example:
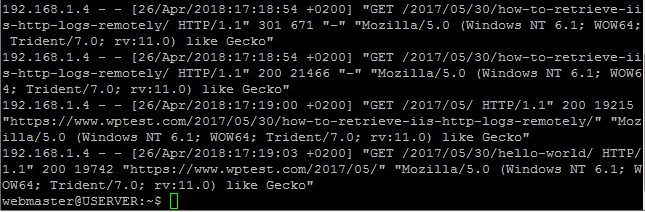
You can use the openssl command-line program to verify that an OCSP responseis sent by your server:
The following sections highlight the most common situations which requirefurther modification to the configuration. Refer also to the mod_ssl reference manual.
If more than a few SSL certificates are used for the server
OCSP responses are stored in the SSL stapling cache. While the responsesare typically a few hundred to a few thousand bytes in size, mod_ssl supports OCSP responses up to around 10K bytes in size. With more than a few certificates, the stapling cache size (32768 bytes in the example above) may need to be increased. Error message AH01929 will be logged in case ofan error storing a response.
If the certificate does not point to an OCSP responder, or if adifferent address must be used
Refer to the SSLStaplingForceURL directive.
You can confirm that a server certificate points to an OCSP responderusing the openssl command-line program, as follows:
If the OCSP URI is provided and the web server can communicate to itdirectly without using a proxy, no configuration is required. Note thatfirewall rules that control outbound connections from the web server mayneed to be adjusted.
If no OCSP URI is provided, contact your Certificate Authority todetermine if one is available; if so, configure it withSSLStaplingForceURL in the virtualhost that uses the certificate.
Apache Web Server Ssl
If multiple SSL-enabled virtual hosts are configured and OCSPStapling should be disabled for some
Apache Web Server Self Signed Certificate
Add SSLUseStapling Off to the virtual hosts for which OCSPStapling should be disabled.
If the OCSP responder is slow or unreliable
Several directives are available to handle timeouts and errors. Referto the documentation for theSSLStaplingFakeTryLater,SSLStaplingResponderTimeout, andSSLStaplingReturnResponderErrorsdirectives.
If mod_ssl logs error AH02217
In order to support OCSP Stapling when a particular server certificate isused, the certificate chain for that certificate must be configured. If it was not configured as part of enabling SSL, the AH02217 error will be issuedwhen stapling is enabled, and an OCSP response will not be provided for clientsusing the certificate.
Refer to the SSLCertificateChainFileand SSLCertificateFile for instructionsfor configuring the certificate chain.
